Amazon.com: Data Security in Cloud Storage (Wireless Networks): 9789811543739: Zhang, Yuan, Xu, Chunxiang, Shen, Xuemin Sherman

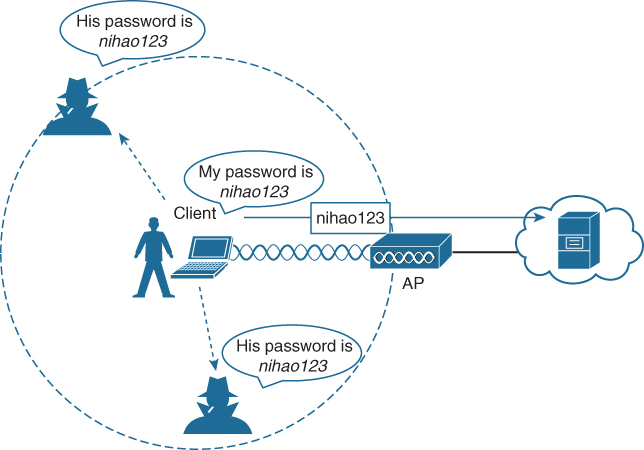
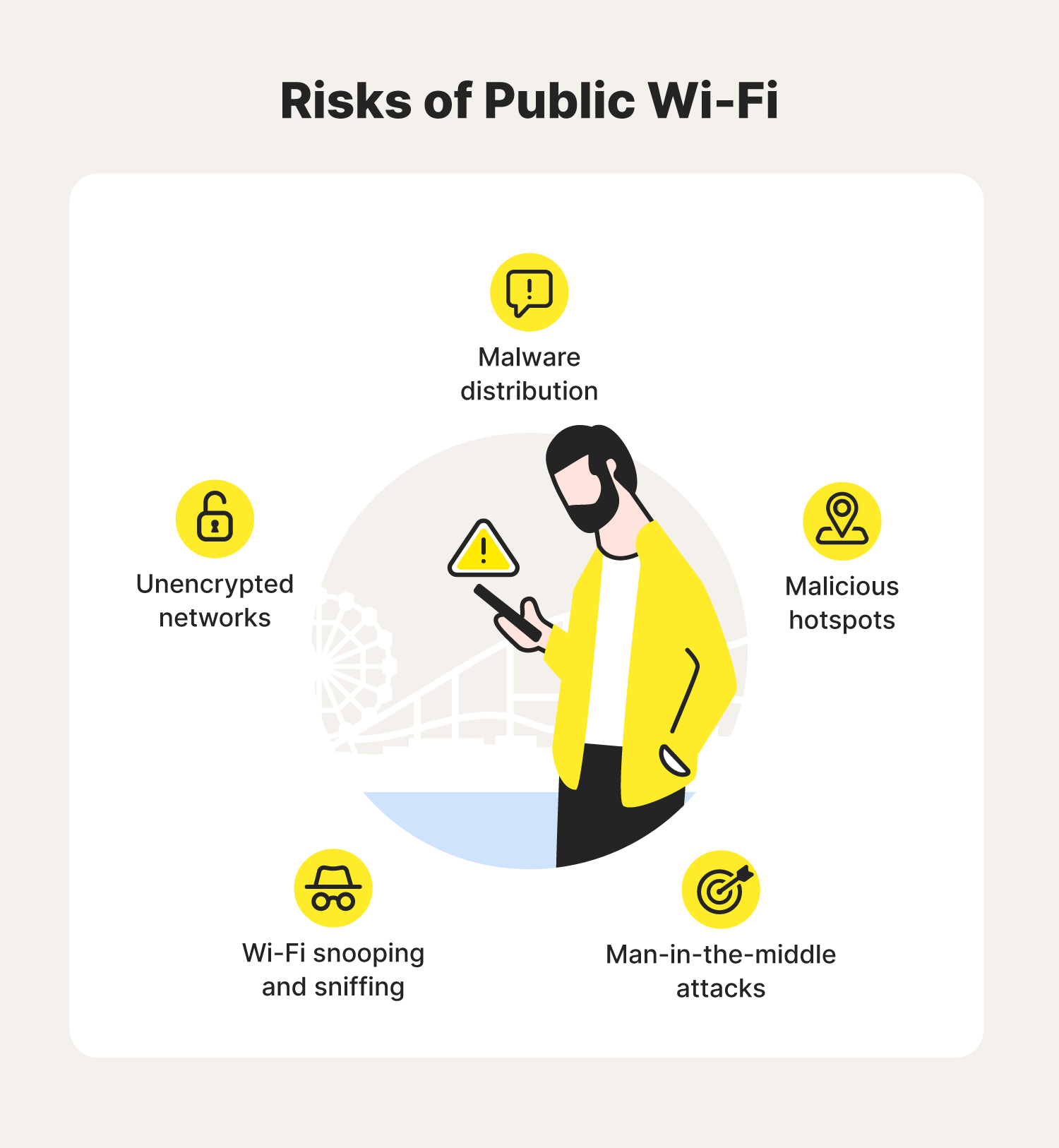
Protecting Yourself from Cybercrime Dangers: Harden Your Wireless & Bluetooth Connections and Use Public Wifi With Extreme Caution – AvoidAClaim: Claims Prevention & Practice Management for Lawyers